CyberDefenders - RE101
Table of Contents
RE101 challenge is a binary analysis exercise - a task security blue team analysts do to understand how a specific malware works and extract possible intel.
Category: Malware Analysis
Tools: - IDA - Ghidra - Cutter - HxD - zipdetails
Questions
Q1: File: MALWARE000 - I've used this new encryption I heard about online for my warez; I bet you can't extract the flag!
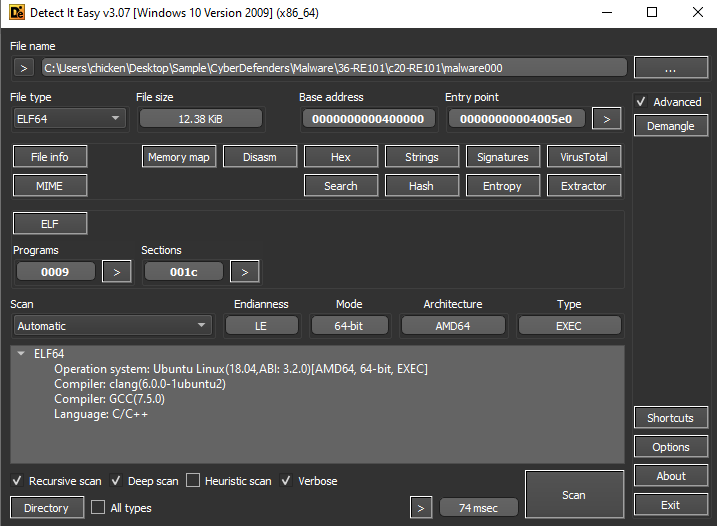
Its elf file compiled by GCC so we can use decomplier like Ghidra to decompile and read the code
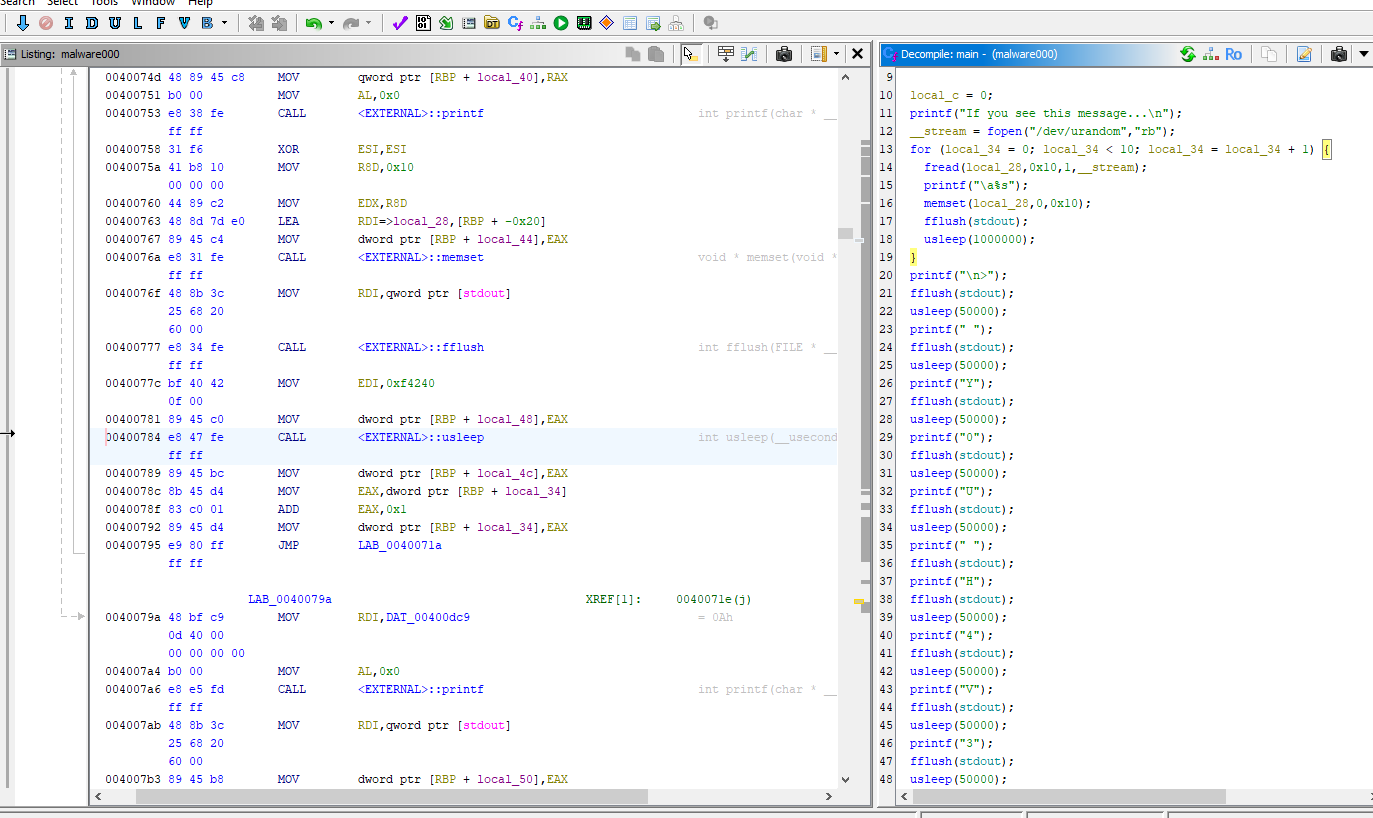
We can see that if we actually execute this file, it will print something and sleep for a several times before actually exit the program
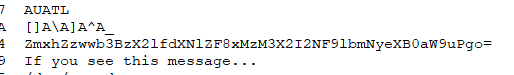
But the flag can be obtained by using strings then we will have this base64 string
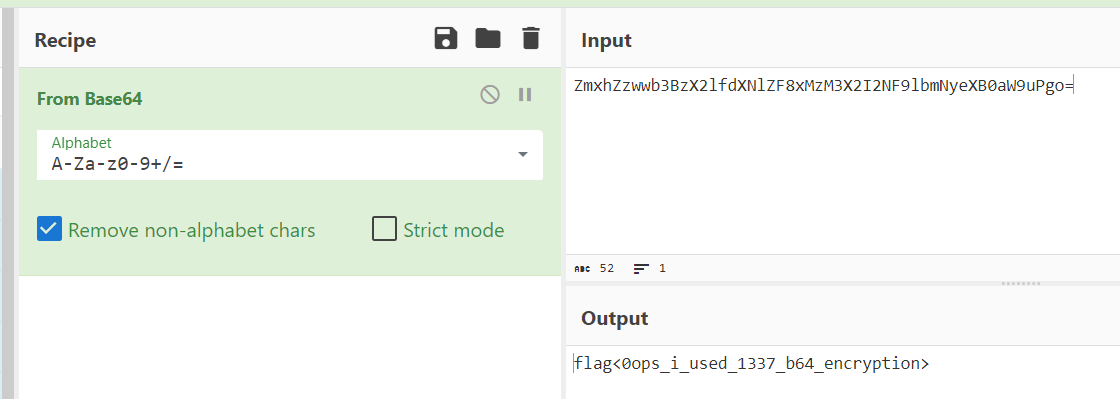
Decode it then we will have a flag
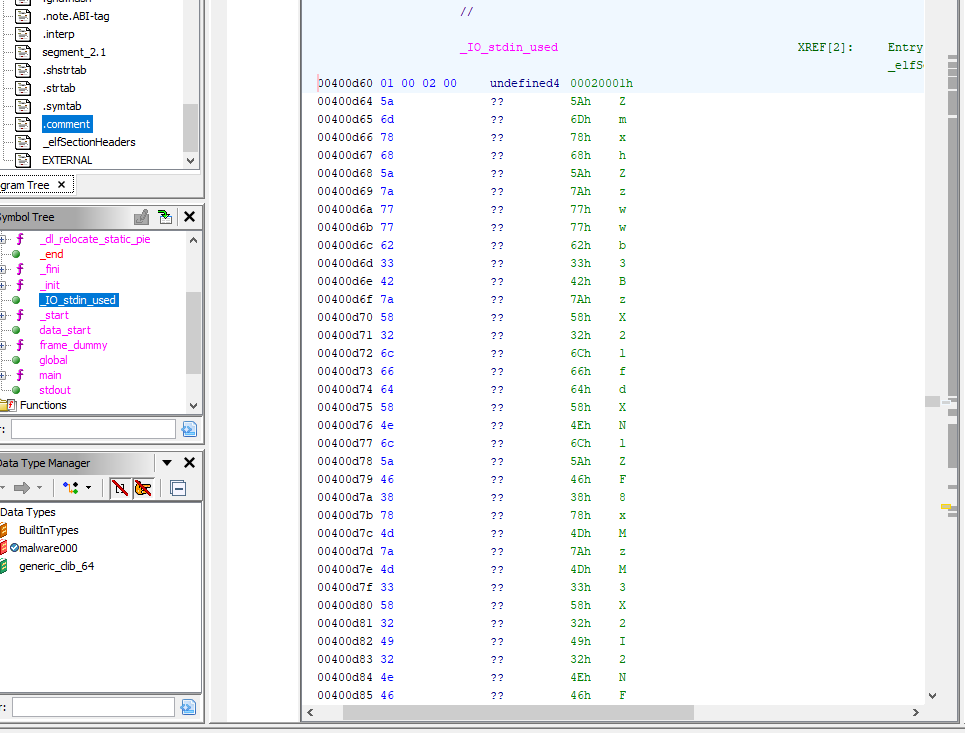
We can actually find base64 character here but strings would be the best to solve this one
0ops_i_used_1337_b64_encryption
Q2: File: Just some JS - Check out what I can do!
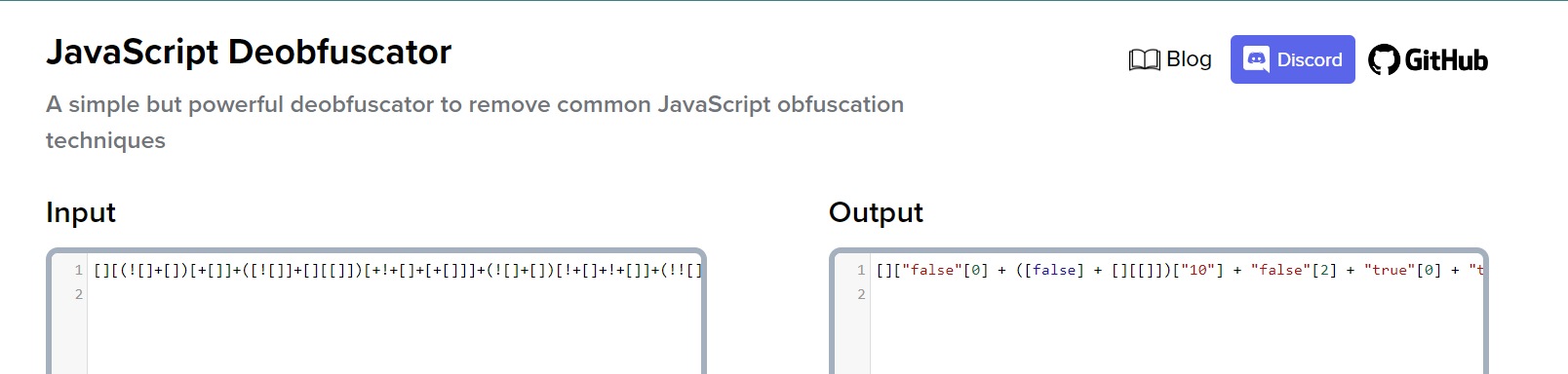
After examined that code, It does look like heavily obfuscated JavaScript so I used JavaScript Deobfuscator to see if I can execute this script directly on the browser, and the output shows us that its safe to execute this JavaScript code and obtain a flag
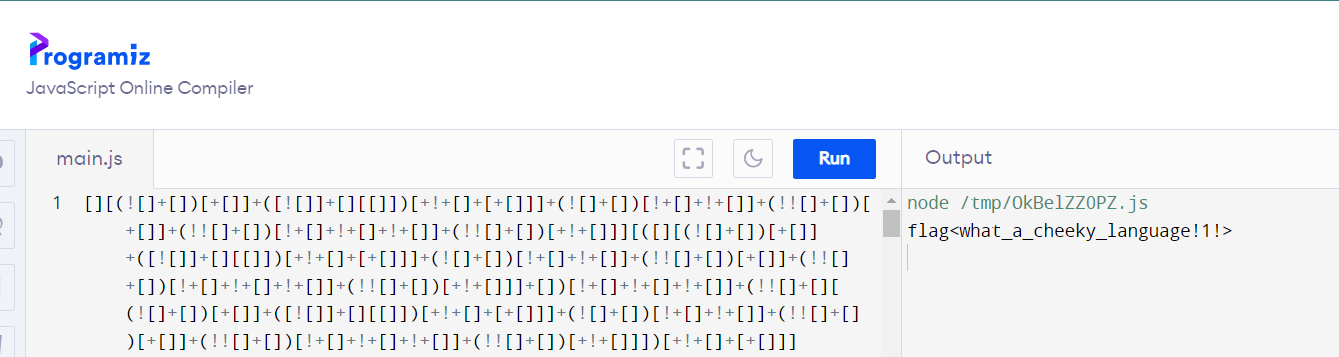
I used JavaScript Online Compiler to execute it rather than using console
what_a_cheeky_language!1!
Q3: File: This is not JS - I'm tired of Javascript. Luckily, I found the grand-daddy of that lame last language!
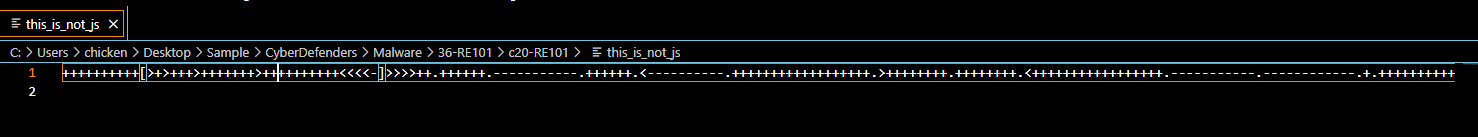
I recognized this pattern, It is brainfuck
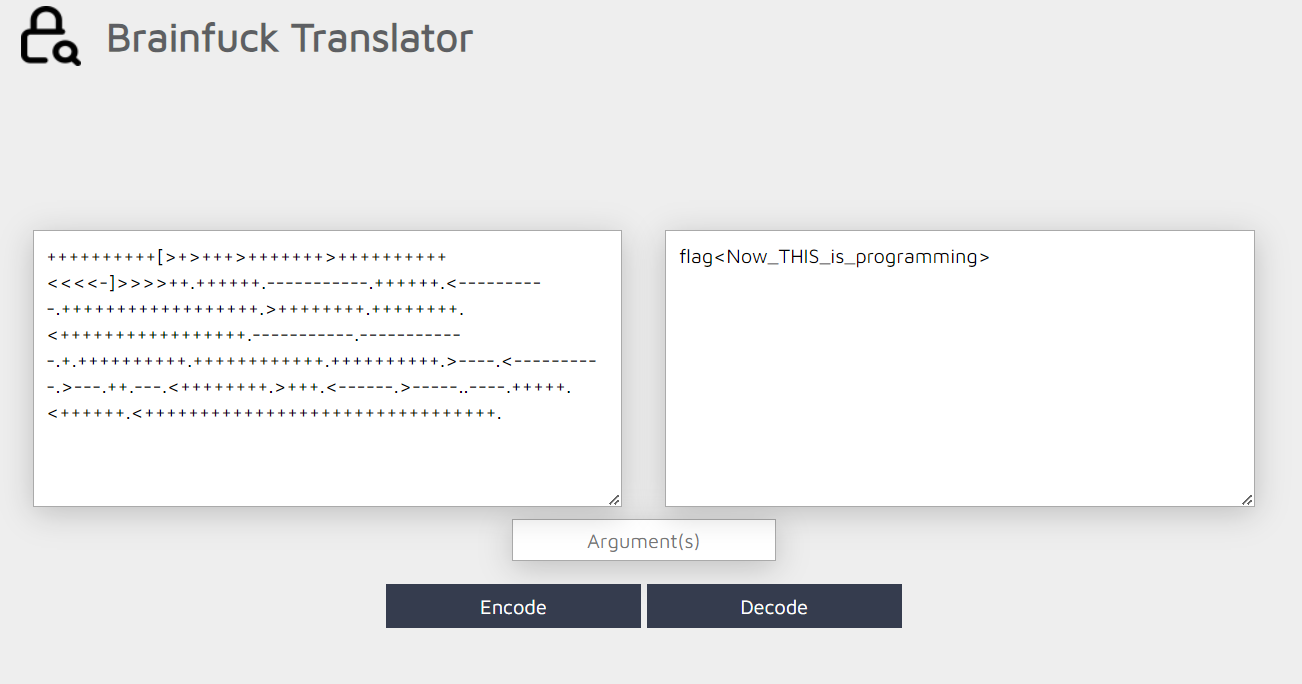
Use Brainfuck Translator to obtain a flag
Now_THIS_is_programming
Q4: File: Unzip Me - I zipped flag.txt and encrypted it with the password "password", but I think the header got messed up... You can have the flag if you fix the file
We couldn't extract a file since file is corrupted so we need to fix it
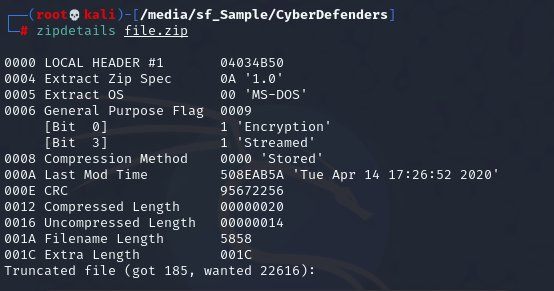
Using "zipdetails" then we can see that magic number of pkzip is correct but Filename Length is a bit weird since we have that "flag.txt" length is not 5858 but 8
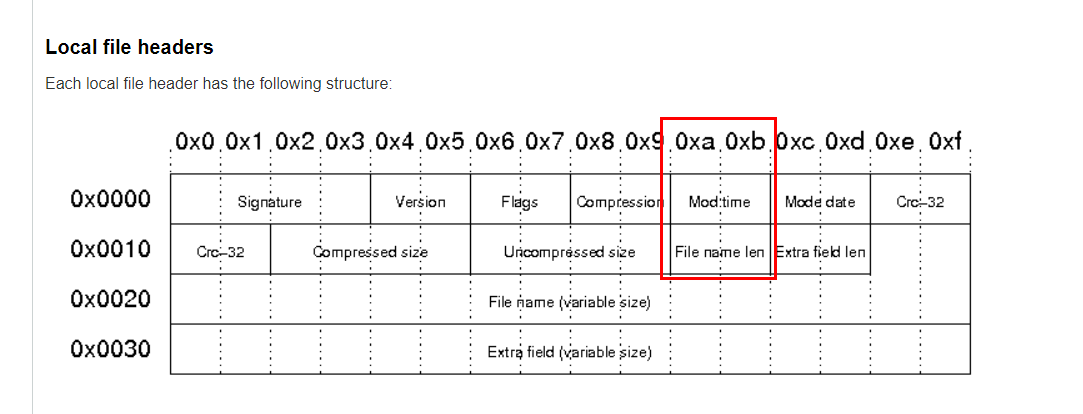
According to https://users.cs.jmu.edu/buchhofp/forensics/formats/pkzip.html, we need to fix this offset
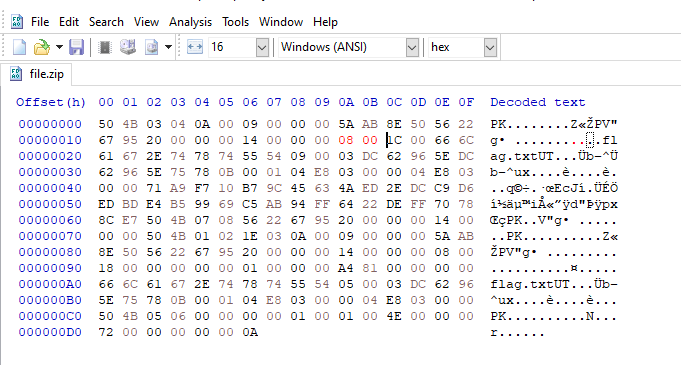
Used HxD (Hex Editor) to fix it to 08 00
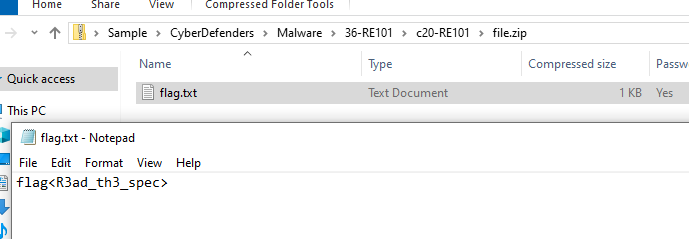
Then we use can password provided from a question to read text file inside recovered zip file
R3ad_th3_spec
Q5: File: MALWARE101 - Apparently, my encryption isn't so secure. I've got a new way of hiding my flags!
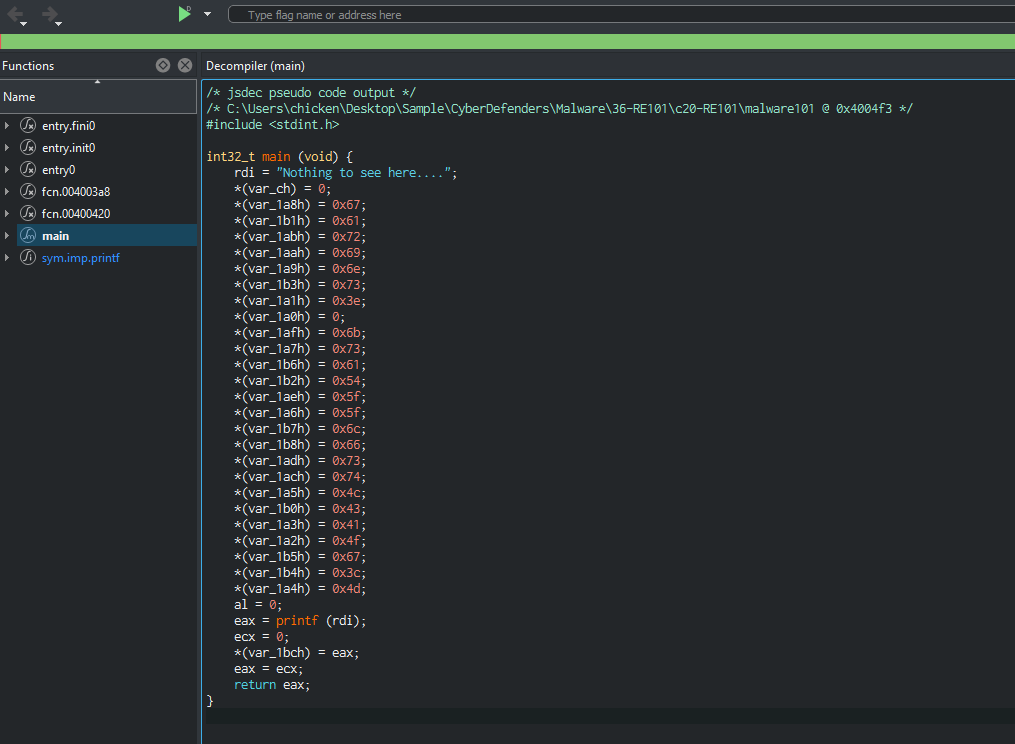
Using decomplier, we can se that many characters will be assigned to different memory location
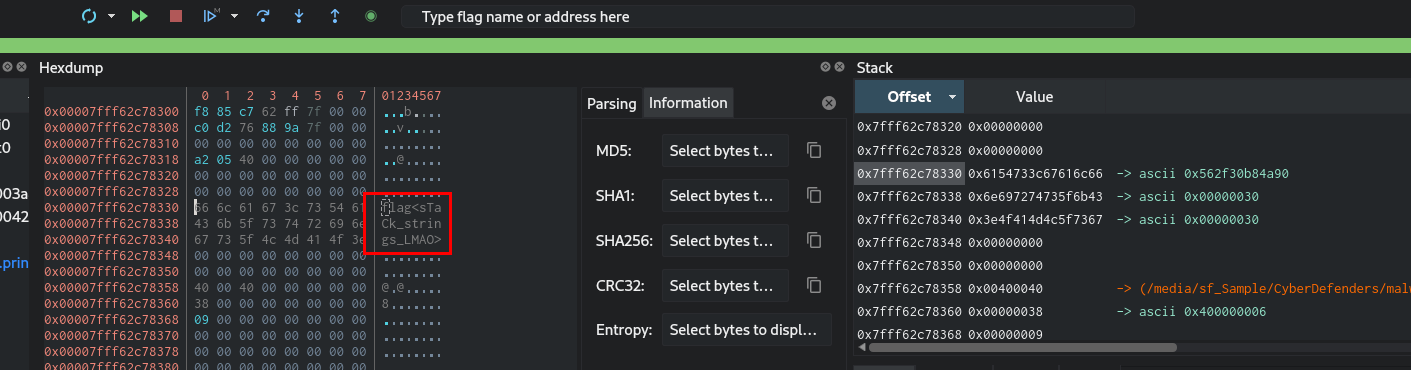
Debug it then open stack memory which we will obtain a flag here
sTaCk_strings_LMAO
Q6: File: MALWARE201 - Ugh... I guess I'll just roll my own encryption. I'm not too good at math, but it looks good to me!
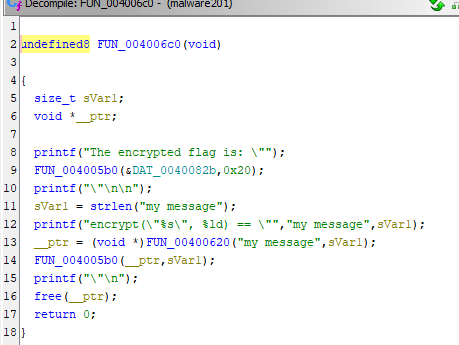
Using decomplier, we can see it will print encrypted flag first then it shows us the sample text which will be sent to encrypt function and print it out for us
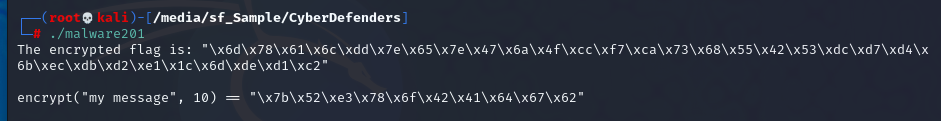
Here it what it look like when we actually executed this file
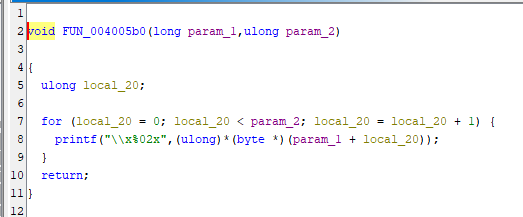
Here is the function that created an encrypted flag but we didn't need it since we can just copy encryped flag from an image above
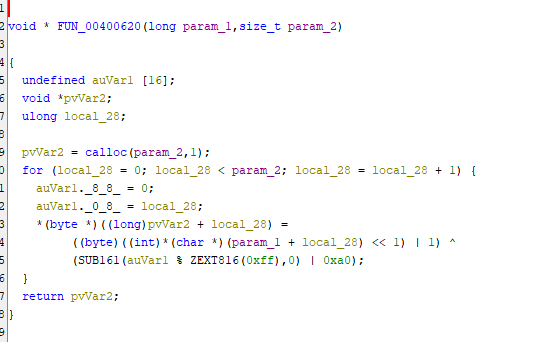
And here is an encryption function, we can see that it start by shifting 1 bit then OR with 1 then XOR the result with (local_28 % 0xff | 0xa0) before getting that output
def reverse_transformation(transformed_data):
original_data = bytearray()
for index, byte in enumerate(transformed_data):
# XOR the byte with (index % 0xff | 0xa0)
xor_value = (index % 0xff) | 0xa0
byte ^= xor_value
# Remove the least significant bit set by the original transformation
byte &= 0xFE
# Right shift by 1
original_byte = byte >> 1
# Append the original byte to the result
original_data.append(original_byte)
return original_data
# Example usage
transformed_data = bytearray(
[0x6d, 0x78, 0x61, 0x6c, 0xdd, 0x7e, 0x65, 0x7e, 0x47, 0x6a, 0x4f, 0xcc, 0xf7, 0xca, 0x73, 0x68,
0x55, 0x42, 0x53, 0xdc, 0xd7, 0xd4, 0x6b, 0xec, 0xdb, 0xd2, 0xe1, 0x1c, 0x6d, 0xde, 0xd1, 0xc2]
)
original_data = reverse_transformation(transformed_data)
print("Original data:", original_data)
print("Original data (hex):", original_data.hex())
I asked ChatGPT to write me this script so we can execute it and get the flag right away
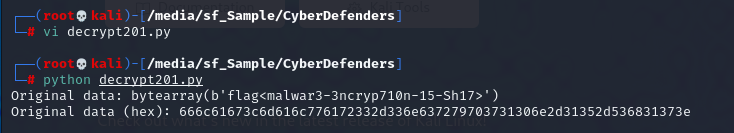
malwar3-3ncryp710n-15-Sh17
https://cyberdefenders.org/blueteam-ctf-challenges/achievements/Chicken_0248/re101/